Section.6 The Matrix

Shadowrun's Matrix rules have changed more than any other major subsystem in the game. They have changed more than any minor subsystem in the game. They have probably changed more than any subsystem in any game. That's a pretty big claim, but I don't
think it's hyperbole. I can't think of any set of rules that has undergone more frequent and thorough revision. And that includes martial arts rules in GURPS. Every edition has produced their own Matrix rules from scratch, which before fifth edition was 1st edition, 2nd edition, 3rd edition, 4th edition, and 20th anniversary edition. All of those had Matrices which were rewritten not just in content, but in concept. In addition, there were four Matrix splat books, which unlike the Grimoire did not content themselves with merely adding content and advancement options, but instead rewrote many key concepts and took the entire system in new directions. That's Virtual Realities, Virtual Realities 2.0, Shadowrun: Matrix, and Unwired. On top of that, there were Matrix related books that produced new rules like Target: Matrix, new Matrix rules hidden all over the fucking place in location books like Tir na nOg and the Denver box set, and a plethora of adventures that basically made their own mind machine interface rules like Brainscan and Mercurial. And of course, the Matrix
fiction in books like Emergence, System Failure, and Psychotrope don't actually match this shit even a little bit. So Shadowrun 5 has its own ground up Matrix rewrite. This is not in any way a surprising fact.
This massive turnover of rules is partially because no edition of Shadowrun has managed to have a set of rules for hacking that weren't terrible. While the Hacker has always been presented as one of the three core archetypal concepts of a character, the rules have
never delivered. But probably the other issue is that there has never been solid agreement as to what exactly the game is supposed to be emulating. For combat or driving, it's clear what is supposed to be going on, but for computer hacking it really isn't. The only thing that has ever been really nailed down is that whatever the fuck is actually going on, there's a virtual reality skin layered on it so you experience conflicts in the Matrix kind of like fights in Tron. But beyond that, it's anyone's fucking guess.
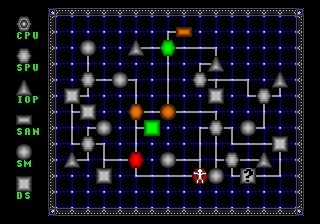
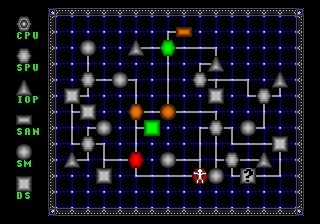 Sometimes hacking computer systems has been represented like a dungeon crawl through the actual pieces of the computer being hacked. How that was supposed to go backwards towards the players being hacked in return is anyone's fucking guess.
Sometimes hacking computer systems has been represented like a dungeon crawl through the actual pieces of the computer being hacked. How that was supposed to go backwards towards the players being hacked in return is anyone's fucking guess.
Anyway, for Shadowrun 5, the Matrix chapter is basically written by Aaron Pavao. This is a
bad sign. He wrote a good chunk of Unwired and the entire Matrix chapter for Shadowrun 4A. He has written at least nearly as much Shadowrun Matrix material as anyone else alive, and it's all bad. It's really,
really bad. Now, I don't like Aaron. I detest him as a writer and as a human being. If and when my wife and I have children, Aaron would not be allowed to be around them unsupervised. Not because I am aware of him breaking the law, but because he has done things that imply that he has urges that I find disgusting. He's also one of the very few people I ever had to block on dumpshock back when I was there, because he kept sending me weird and aggressive personal messages. That man is genuinely creepy. But that is not why this chapter gets such low marks from me. I find this chapter to be unacceptable dog vomit because it's incoherent warmed over shit on its own merits, of which there are none.
To have any
hope of understanding this chapter, you need more history. When the Matrix first happened, it was envisioned as a thing that traveled along fiberoptic cables. You had a “jack” in your head and you plugged your brain into a cyberdeck and you plugged your cyberdeck into the wall and the wall plugged into the target computer. The concept was that the Decker would plug in and do their hacking, fighting the enemies in cyberspace while the other characters did their part of the run in meatspace and the two would interact sometimes and everyone was even acting in the same initiative counts, so the Decker's victories and defeats would have immediate consequences in what the other characters were doing and vice versa. This is a kind of cool sounding setup, and most old Shadowrun hands can probably name a couple of times when it actually worked out and delivered some nail biting scenarios. But that's not much to show for 15 years of gaming. In the vast majority of circumstances, there was precious little reason for the Decker to do his thing simultaneously with the other team members doing theirs, and instead the whole thing ended up be a shitty game of splitting the party and waiting for other team members to complete their solo quests. And in 4th edition they declared that enough was enough and also no one has a land line anymore because it's two thousand and fucking five, and made things wireless. The idea was that the Hacker would then
have to run around with the rest of the team doing his shit in real time because the hacking itself was short range and line of sight. You had to get to the door to hack the door, and so on. And you could certainly imagine how this might solve the core issue of getting the Hacker to actually play the same game as the rest of the team.
But with new ideas came new problems. There were simply mechanical and implementation problems of course: hacking into nodes was a damn extended test, which as we covered previously are an unnecessarily time consuming yet annoyingly deterministic portion of the rules where you roll a whole fuck tonne of dice over and over again and eventually the thing you knew was going to happen happens. The whole system was based on your equipment ratings to the point where actually
being a hacker essentially didn't matter during the actual matrix actions – you just
owned stuff that rolled giant piles of dice against other stuff. That shit was easy to fix. Much worse were the
conceptual problems: Hackastack, Agent Smith, Dropout, Hall of Mirrors. Let's go through those:
- Hackastack: If I hack things by bringing my computer into range of the target and pressing the “Go” button, why wouldn't I bring two computers? Or eight? Or twenty eight? Shadowrun is a post-industrial society, if bringing more processors to the fight is a thing that would be helpful, I can do that.
- Agent Smith: If there are autonomous or semi-autonomous programs that can do stuff for me, why can't I make copies of those programs and run each copy on another computer in my Hackastack doing those things for me dozens if not hundreds of times?
- Dropout: If enemy hackers affect the field of battle by wirelessly hacking into our equipment through active wireless antennae, why don't we just turn the wireless antennae on all the important shit off during missions? And if people do in fact do that, why is the hacker able to accomplish anything of note, considering that the wireless on everyone's important shit is turned off during the mission?
- Hall of Mirrors: If you have to roll dice to affect each node one by one, and each device can have its own node, can't the hacker be stymied (or at least have their entire subsystem grind to a halt) just by putting up a lot of nodes? A ten layer onion would take all night to roll the dice to penetrate, and what's actually stopping you from making it a two hundred layer onion?
So that was the state of things when Aaron stood up to claim that he in fact did have the solution and began working on Unwired to update SR4 and fix those holes. Spoiler alert: he did not. Unwired was a pooh stick. Probably the worst sourcebook for 4th edition. An edition that had the 4th edition Runner's Companion made for it (although come to think of it, Aaron's AI rules were a noticeable part of why that book was so bad, so there's a theme).

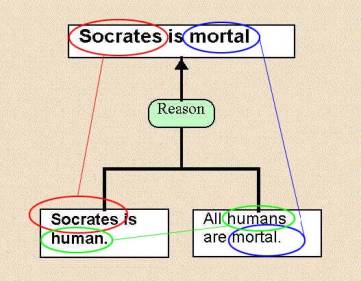
This is in fact where I, Frank Trollman, came in and gave my “Momhammer” speech about how Dropout was essentially an unsolvable problem without a radical redesign of how things worked. In order to create a scenario in which hacking fights made any sense at all, you would have to keep people from dropping out. The two possibilities for handling that were what I called the “Stick” and the “Carrot.” The
stick approach was the one I favored, was that you straight up could not drop out. Even if you shut your devices off entirely, even if you
threw them away, hackers could still fuck with you directly with the trode technology that had already been established to exist. The
carrot approach was to create a Nash equilibrium where people
voluntarily allowed the hacker access to their important things by giving people advantages for having current wireless connectivity that were sufficiently good that the risk of hacking was acceptable. This, I pointed out, was
insanely difficult and essentially impossible, because you have to make it so that the hacking actions are worth using against the devices that people allow hackers to hack, while still making the bonuses for turning wireless on attractive enough that people use them
even though there are hacking actions worth using. And Aaron and Bull insisted that they
totally could do a carrot system that worked and they would totally show me some day. Which wouldn't even be worth mentioning, except for the fact that when Jason (the development lead) gave the Matrix preview for this edition, he laid it out as a carrot system using exactly the nomenclature I had defined all those years ago. Meaning that this entire chapter is literally just a giant middle finger pointed at me personally – the authors of this edition setting out to prove me wrong for saying that they couldn't successfully make a functioning system that worked like this. Spoiler Alert: I was and am right on that point, and this entire chapter serves as nothing more than a giant turd that I can glance at meaningfully as if to say “I told you so.” Because I fucking did.
Anyway, on to the chapter...
The first page is to get you psyched up for computer hacking. A combination of Poochie the Dog and like a stoned Carl Sagan attempting to explain that the virtual computer world is both marvelous and also transgressive. They also attempt to get the 4th edition “Hacker” nomenclature to play nice with the 1st edition “Decker” nomenclature by claiming that “Hacker” means both Technomancer and mundane computer user, while “Decker” means just the non-technomancer Hackers. Like all the rest of the complicated Central to the idea that a Decker is a good thing to have on your team is that he can fight other Deckers. And in the words of this chapter “Quick tip: leaving yourself vulnerable is a bad idea.” Now that's actually a stick argument, and not a carrot argument at all. You're supposed to bring a hacker because otherwise you don't have defense against hackers. But this is
not true. As the developer himself said, this is an attempt at a carrot system, so the first page introduction is fucking lying to you.
What follows is a two page lexicon for this chapter. There are a couple of things I want to say about that. The first is that if your subsystem has two pages of dense text just to define terms, it is probably too fucking complicated. More subtly, this section is actually called “Matrix Jargon” while the previous lexicon was called “Shadow Slang.” This means that even by word searching the pdf it is very difficult to find all the terminology lists. And finally, a bunch of the important pieces of matrix terminology like “jack” and “dumpshock” are actually in that previous piece of shadow slang and not in this matrix jargon thing. So it's two pages long, it's hard to find, and it doesn't even cover all the special terms this chapter is using.
So the first presentation of what the Matrix is and what it looks like also causes the entire chapter to crash and burn. Everything, and I do mean
everything is an “icon.” Every piece of hardware, every piece of software, every datafile, every social construct,
everything. When I want to send a message to my friend, I tap a little icon with the shortcut to their commserver, and that's an icon. It's next to my comm program, which itself is an icon, and that's attached to my commlink which is also an icon in the Matrix. So just the fact that I have a future phone with some numbers in it means that right next to my meatspace body are dozens if not hundreds of icons. Any icon can be made to look like whatever you want it to, and to really find out for sure what any icon represents requires an action for that
one icon. So right away, on a
Hall of Mirrors basis alone, this system is completely unplayable. No person or group has ever in the history of the world played even a simple hack by the rules as written, and noone ever will. It's impossible. Before you can even get to “I would like to hack the lock” you're supposed to spend hundreds if not thousands of actions sifting through all the RFID tags on the snacks in the vending machine in the corner. It's completely fucking insane.
 It takes an action and a die roll per icon to find out what the fuck is going on. There are thousands of icons. Therefore go fuck yourself. That's logic.
It takes an action and a die roll per icon to find out what the fuck is going on. There are thousands of icons. Therefore go fuck yourself. That's logic.
The next thing that they tell you is that they have a workaround for the Hall of Mirrors. See, when you turn on your matrix vision, you have a filter that removes all the “uninteresting” icons. Wait, doesn't that mean that you could label all your rifles and locks and death lasers “underwear RFID system” or some fucking thing and automatically be invisible to all Hackers? Uh... yes. Yes you could. And people can attempt to see through this chicanery by... analyzing each and every fucking icon to see if it's “really” trivial bullshit or not. And then we're right back into the fucking Hall of Mirrors! This rabbit goes down really far, but it doesn't ever get any better.
Now, if people actually attempt to play this fucking thing, what they actually do is ignore all the icons that aren't important and only roll for the ones that are. This is still intractable, because the number of plausibly important icons is
still fucking ridonkulous, but at least it's something. What ends up happening is some sort of bizarre game of Go Fish where the player has an idea of what he wants to do and then the GM tells them if there are any icons around matching that description.
OK, so the next thing that's important is the core icon of the player character: the Persona. These represent “you.” But they aren't necessarily
part of “you,” they can be created by your computer while you are operating it in AR or even not physically touching it. So um... yeah. There's actually no limit to the number of times “you” can be in the Matrix at the same time. You need a piece of real hardware each time you want to duplicate yourself, but
Hackastack to your heart's content.
This version of the Matrix is all about “Marks.” That stands for something, and you don't care. Basically, if you can mark something, you can access through the matrix. This was probably supposed to solve something, but in reality it just adds an extra layer to your accounting for everything. There is another thing involving “Grids” which is your wireless service plan. Yes... really. So the fact that one Hacker is on Verizon and another Hacker has AT&T is supposed to matter. And um... this works for Technomancers
how? And they also want to talk about “AROs” which are exactly like “icons” except they have a cooler name and this fucking book needed more specialist nomenclature to confuse the reader with.
Anyway, the nominal purpose of the Grids is so that GOD can come and kick your ass if you get uppity. I'm actually serious. There's this organization called the “Grid Overwatch Division” and it is in charge of watching the grid and putting the smackdown on people who fuck with it. You may wonder how the fuckity fucksticks that makes any sense if the matrix is a fucking mesh grid and you're a fucking hacker whose job it is to do industrial espionage so presumably you aren't logging onto T-Mobile
anything and just hacking things in your direct vicinity by logging onto them directly. And um... hmmm....
After spending ten pages describing how the Matrix works and dropping heaps of specialist nomenclature on you, it gets to the point of telling you what you need to know to play a Hacker. Sorry, it gets to the point of telling you the sections you're going to need to read if you want to be able to find out what you need to know to play a hacker. Half a page (the rest is taken up by floating example box texts), and it includes twelve page citations. Seriously. Twelve. It wraps onto the next page because of all the extraneous crap squeezing the main text and there are four more page citations. And there's a box text of the “quick” things you need to know about cybercombat which has five more page citations. Just think, in this less than a page worth of stuff, we could have been spared more than twenty page citations had the information of this chapter instead been presented in a logical order.
So you have skills and you have attributes, but your devices
also have attributes, and those are analogous to attributes in how they are rolled but not analogous to any of your attributes because go fuck yourself. Devices have up to four Matrix Attributes, but legal devices tend to only have 2. But here's the “best” part: your device's Matrix attributes change dynamically during play. You can reconfigure your deck on the fly to be more attacky and less data processish or whatever. This makes things considerably more complicated, but remember that you can also just have a hackastack of decks, so whatever. The most mysterious thing on the cyberdeck chart is an entry labeled “Programs.” Many people believe this to be the elusive “program slots” which are mentioned only three times in the book: once when it tells you that you can switch programs into and out of your program slots, once when it tells you that Agents take up a program slot, and once when it tells you that you get a couple extra program slots for every fucking Drone you have. So if you are suspecting that we're looking at an incredibly cheap Hackastack platform from which to launch an Agent Smith armada... you're probably thinking right. If, however, “Programs”
is the hard cap for how many programs you can use at a time, then things are super fucked for everyone who hasn't figured out the Drone based hackastack. Cyberdecks with a program limit higher than 1 can't be had for less than 100,000¥. On the other hand, you can have extra Matrix Programs for every Shiawase Kanmushi you happen to have: they are bug-like crawler drones that fit in your damn pocket and cost 1,000¥ each.
Shadowrun 5 wrote:The greatest ninjas in the world can’t walk through the desert without moving some sand
That's supposed to sound like wisdom, but this game has the fucking Traceless Walk ability and the Levitate spell. The greatest ninjas in the world actually
can walk through the desert without moving any sand. It's not actually all that impressive of a magical feat. This chapter is filled with stupid, but for some reason this quote made me snort beer into my nose. It wholly encapsulates the entirety of this chapter: make absolutist pronouncements without thinking them through, totally ignore the realities of the setting when stating things, generally make a total ass of itself all the time at every opportunity. This is to introduce the Overwatch Score, which is a whole set of secret accounting to determine if and when the GODs come and turn you into a gooooon for violating matrix protocols. The easiest way to handle this is to hackastack and run your bullshit through a bunch of different icons, because the overwatch score sticks to whatever icon is performing the action, not to the region or “you” in any meaningful sense. When your Overwatch Score gets high enough, you explode because GOD hits you for a giant pile of matrix damage arbitrarily without using the actual hacking rules. But while this would be very bad, it also never has to happen because fucking around with three card monte resets your overwatch score in any case. It's a perfect storm of bad rules. It's fiddly, it requires unacceptable amounts of accounting on both sides of the GM screen, it's ridiculously heavy handed, and it makes no fucking sense. How the fucking hell do these guys operate in the secret corporate enclaves you will presumably be performing hack actions? If they can do that at all, why can't corporate defense spiders nuke you with GOD death spam whenever they spot you? What the actual fuck? And of course, at the end of the day it's all meaningless because the same spider pockets that get you around the (possibly) ridiculously draconian program slot caps also get you around the insultingly draconian GOD convergence storm as well.
Mark accounting makes no sense. There's some wibbly wobbly timey wimey stuff about why you can't let other people use your marks... and it honestly reads like a temper tantrum. Someone pointed out that the entire thing about recognition keys was just bullshit that wasn't really different from passcodes and solved zero problems. And then Aaron stamped his foot and insisted that you couldn't share them
because he said so. It's dumb.
There are thirty distinct Matrix actions that are listed in the matrix actions section. Seriously. Thirty. This doesn't include all the actions like swapping programs and reconfiguring your deck stats and shit that are written up elsewhere in the chapter, nor does it include any of the drone operation actions performed through the matrix, nor does it include the special actions of all the programs. It's four and a half pages of matrix actions. It's far more complicated than it needs to be, and I'm going to down my slivovice rather than list them all. There's a page that lists the Matrix Actions in a table, and for some reason it is labeled “Matrix Action Indices” despite the fact that there is only one of it and it doesn't tell you what page the long form description is on for any of them.

There are 26 programs. Many of them appear to be written under the assumption that players are going to have considerably more than one active at a time. A lot of them are just +1 bonuses to things. It's all very clumsy. One thing that I will say is an improvement is that programs don't have ratings. I mean, it basically invalidates having programs
at all because there are no good or bad programs, but there is one piece of inane micromanagement that has been done away with. The program list doesn't include the 14 flavors of IC, nor does it include Agents or Autosofts. And those things all have ratings, so the software rating is totally in there, it's just that arbitrarily those 26 pieces of software don't have ratings.
Technomancers have their own set of shit. Technomancers are kind of like mages, in that they summon spirits (called sprites) and cast spells (called complex forms) and have their own special attribute that works just like magic. But all their shit happens in the matrix. There is absolutely nothing stopping you from being a technomancer who also uses Decker tools, and indeed you're going to have to because the technomancer toolbox isn't complete and you can't know all the complex forms anyway. If the Matrix rules were transformed into something that was actually playable, Technomancers would be either way better or way worse than regular mundane hackers depending on how their shit got converted to a functioning system. As is, they are basically the worst characters in the game because they spend really a lot of their character creation budget on interacting with a subsystem that doesn't work. In order to even attempt to understand how technomancers are supposed to work, you pretty much have to read the entire section for mundane hacking, then the fifteen pages on technomancers and then go back and do line by line comparisons between the sections. On even a casual reading I can see that this shit doesn't work, and I lack the willpower to figure out where all the failure points are.
And now we're at the end of the chapter. Riggers get their own chapter and it's of course highly related. And you may have noticed that we haven't actually come to the “carrot”
at all. That's because it isn't in this fucking chapter. In this entire chapter we are given zero reasons why anyone who was afraid of being hacked wouldn't just turn their wireless off and walk away. Those “reasons” are given later in the book. Spoiler: each item gets a completely arbitrary bonus for you putting it in harms way of hacckers. Some of these make a little bit of sense, some don't. But what they all have in common is that there are in fact
very few objects that get a bonus for being connected to the internets that are simultaneously worth hacking when they are. In fact, the only thing that comes remotely close is remote controlled killer robots. By and large, the hacker just doesn't have anything to do in combat. Four fucking pages of matrix actions and they don't have anything useful to contribute.